还有 48 小时,我们就将迎来 2026 年的首场苹果特别活动。
而这次活动,是字面意义上的「很特别」,因为它采取了一种苹果从未使用过的新形式。

▲ 图|Reddit
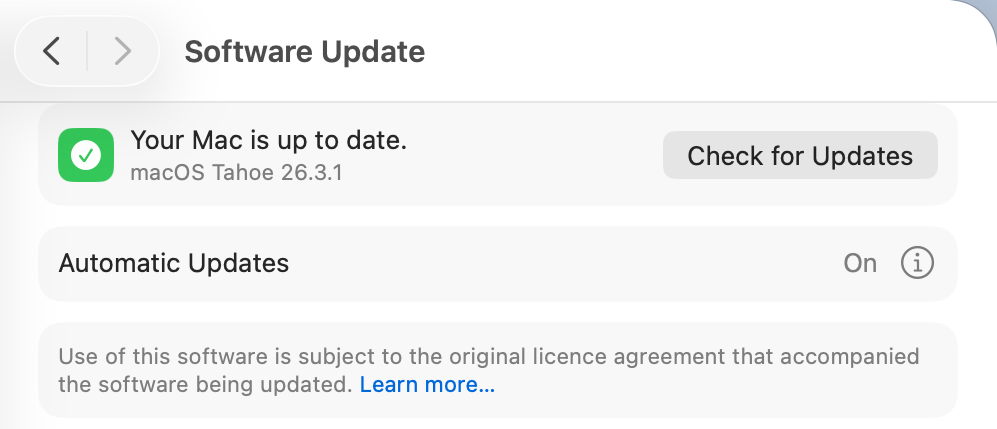
正如爱范儿之前的前瞻,本次发布会的主活动将于北京时间 3 月 4 日晚 10 点举行,届时蒂姆 · 库克会像常规发布会一样上场播片。

但这次活动的期限却不限于 4 号当天。
根据爱范儿收到的资讯:苹果会在今天(2 号)和明天晚上采用「官网上架」的形式,提前公布一部分新品,形成「一天一发布」的节奏,最后在 4 号的主活动上进行统一介绍。
同时,在经历过去年 iPhone 17 系列的强势销量,以及有史以来最好的一次财报之后,苹果对于本次活动同样信心满满。
彭博社的苹果专家马克 · 古尔曼透露:
苹果零售店已经接到了上级通知,要求「在本周上新之后做好迎接大量客流的准备」。

▲ 图|彭博社
还有一些苹果店员工表示,前期的规模「堪比秋季 iPhone 发布会」前的准备工作。
这表明,苹果预计这次 3 月发布会新品上市后的需求会相当旺盛,且至少有一款产品将拥有极高的市场号召力。
至此,我们已经基本可以看出苹果在马年的第一场发布会的大概样貌了:
- iPhone 17e
- MacBook(A18 Pro)
- MacBook Pro(M5 Pro/Max)
- iPad(第 12 代)
- iPad Air(M4)
- 新 Studio Display
- 新 HomePod 和 HomePod mini
- 新 AppleTV
- 其它零星硬件产品
iPhone 17e:便宜,但不一定值
作为苹果关注度最高的一款产品,iPhone 17e 无疑将会是本次发布会的讨论中心之一。

目前,大家对于 iPhone 17e 的期待主要集中在这几点上:有没有高刷屏,能不能用上灵动岛,以及是否支持 MagSafe。
从截至发布会前最后一分钟的爆料来看,今年的 iPhone 17e 在屏幕方面不会有什么明显进步,ProMotion 高刷屏大概率还是缺席。

▲ 图|Threads @privatetalky
而爆料在 iPhone 17e 是否会采用灵动岛上产生了明显的分歧。
各方渠道能够获取的先行信息中,「灵动岛」派和「刘海」派几乎是对半分的——
这其中必然有苹果故意放出的烟幕弹。如果从现实角度考虑,iPhone 17e 继续采用 16e 同款的 6.06 寸60Hz 刘海屏的概率更大一些。

▲ 图|PCMag UK
不过在参数配置方面,iPhone 17e 相比 16e 的提升还是很大的,这也符合 e 系列「买处理器送手机」的传统。
目前基本可以确定的是,iPhone 17e 将会采用 iPhone 17 同款的 A19 处理器,以及当下最新的 C1X 自研基带和 N1 网络芯片。

▲ 图|MacRumors
此外,为了促进竞争力,还有报道指出苹果可能会逆势而行,将 iPhone 17e 的起步容量提升至 256GB,并继续着重「优秀续航」这一核心卖点。
只不过 iPhone 17e 目前最大的对手,既不是疯狂涨价的内存,也不是同价位的安卓机型,而是自家大哥 iPhone 17。
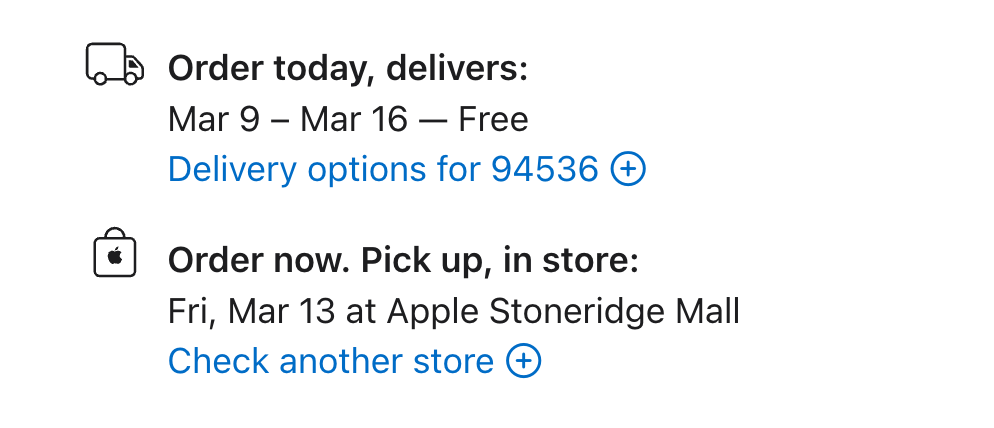
根据最新消息,iPhone 17e 的起售价将会维持 599 美元不变,即国行 4499、国补 3999 元起。

▲ 图|CNN
然而眼下 iPhone 17 和 iPhone Air 国补价格,也都是 5499 元。
前者有双摄、高刷等等升级,后者也有 A19 Pro 和钛合金机身,都是感知非常明显的提升。
因此,爱范儿对今年 iPhone 17e 的评价和购买建议保持不变:
iPhone 17e 属于一台「酱香型」手机,首发全价购买不太值得,更适合等到国补 + 渠道价格进一步下探到 3500 元左右再入手。
MacBook:上网本也有第二春
本次发布会的另一个话题中心就是用 iPhone 处理器的新 MacBook。
实际上,苹果做这一类无后缀名的 MacBook 行之有年了。
从最早的 iBook,到后来的聚碳酸酯 MacBook,苹果一直都有尝试把笔记本打入真正的平价价位。
最后的尝试要到十多年前的 12 寸 MacBook,受限于当时的英特尔 Core M 处理器实在太孱弱,一台「上网本」的定位,上网都不痛快。

▲ 图|TechRadar
而这次的新无后缀 MacBook,作为一款主打极致性价比的型号,它会直接用上 iPhone 同款的 A18 Pro 处理器,所有周边配置也都采用货架库存,主打一个「多快好省」。
那新 MacBook 能实现多快好省吗?你别说,还真有可能。

▲ 图|Yanko Design
苹果内部测试表明:虽然用着落后一代的 A 系列处理器,在更大的机身空间和 macOS 的加持下,新 MacBook 的性能强于 M1 处理器 Mac。
并且它运行着完整的 macOS ——
这意味着对于文档处理、浏览器办公、轻量设计修图而言来说,A18 Pro 的基础性能是完全足够的。

▲ 图|AppleInsider
实际上,这次的新 MacBook 可以看做苹果对于新时代电脑办公设想的一个小缩影:
对于很多「只需要一台笔记本上班」的工种来说,绝大部分的工作其实都是在办公三件套、聊天软件、浏览器/云端 AI 上解决的,并不需要那么强的 SoC 本地性能。
而 A18 Pro + macOS 的组合刚好完美卡进这个区间,并且还能获得标准的 MacBook 屏幕、键盘、扬声器和大电池。

▲ 图|MacDailyNews
考虑到 2026 年国补政策仍将延续,再加上教育优惠,新 MacBook 在国内的实际入手价格可能进一步下探至 3000 元档。
前几代销量已经证明,当 Mac 真正进入「买得起」的区间,潜在用户的转化率会迅速提升——
如果再加上之前发布的 Apple Creator Studio,一台轻薄 MacBook 加上一套准专业级工具,价格甚至不超过一台标准版 iPhone,夫复何求?
MacBook Pro:稳定升级,该买就买
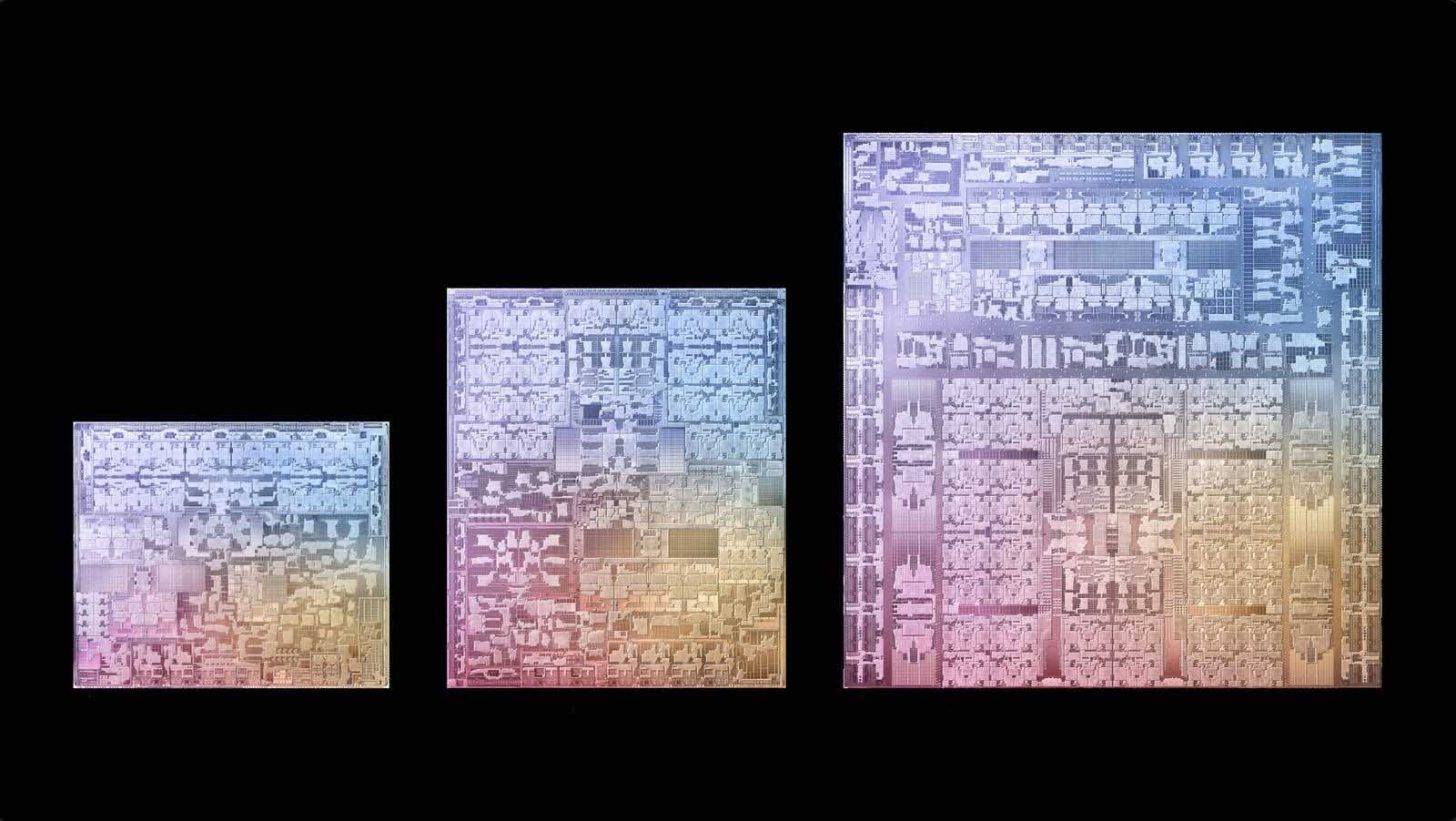
时隔近半年,M5 芯片产品线终于迎来了 Pro 和 Max 两大升级,重点升级依然集中在 GPU 图形能力上。
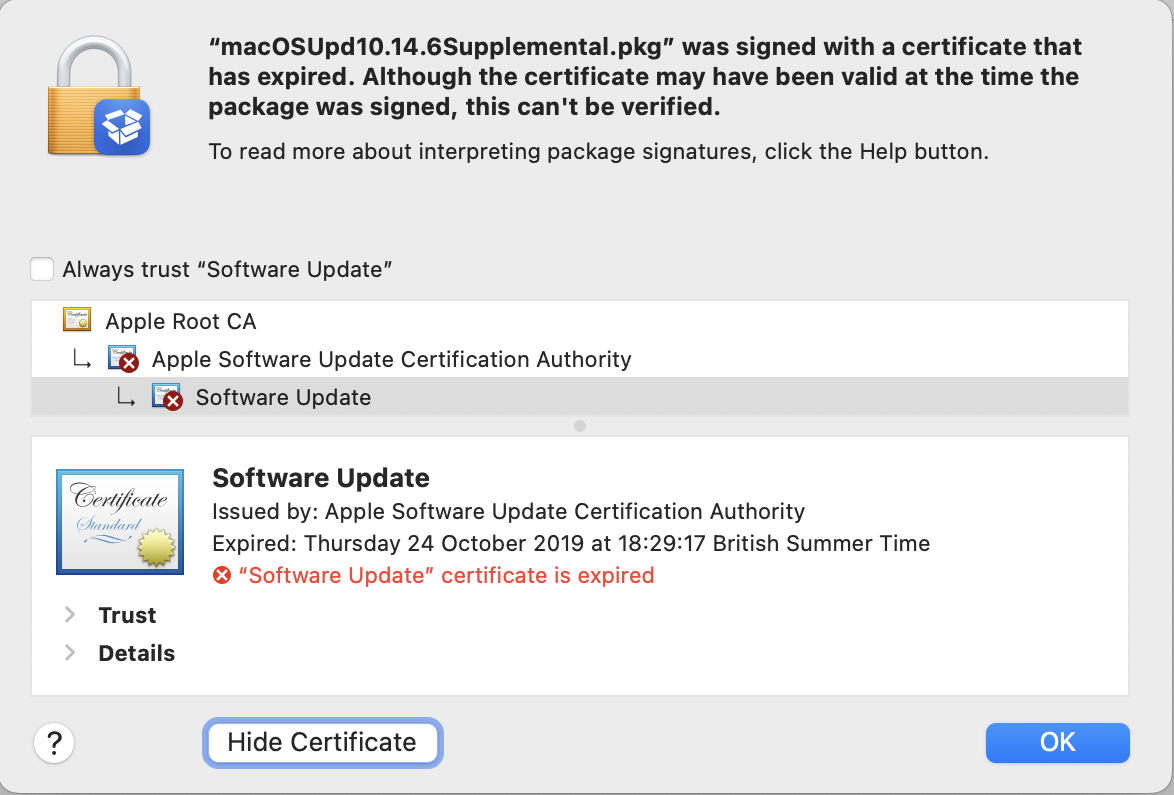
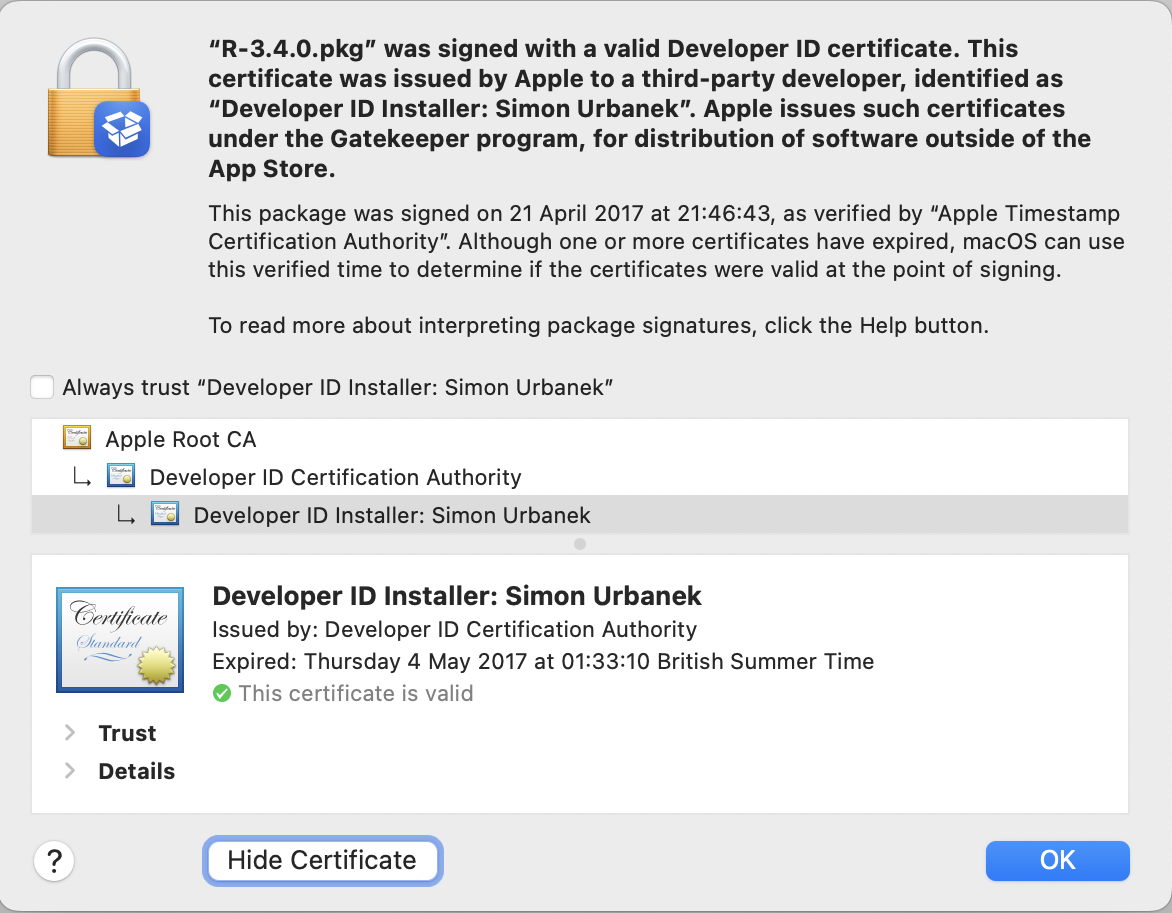
目前我们看到,M4 Pro/Max 款 MacBook Pro 在苹果官网的发货时间已经推迟,这通常是配置更高的新品即将发布的前兆。
根据外媒 MacWorld 的估算,新款 MacBook Pro 的 Geekbench 6 GPU 跑分,极有可能会超过 80 颗 GPU 的 M3 Ultra。
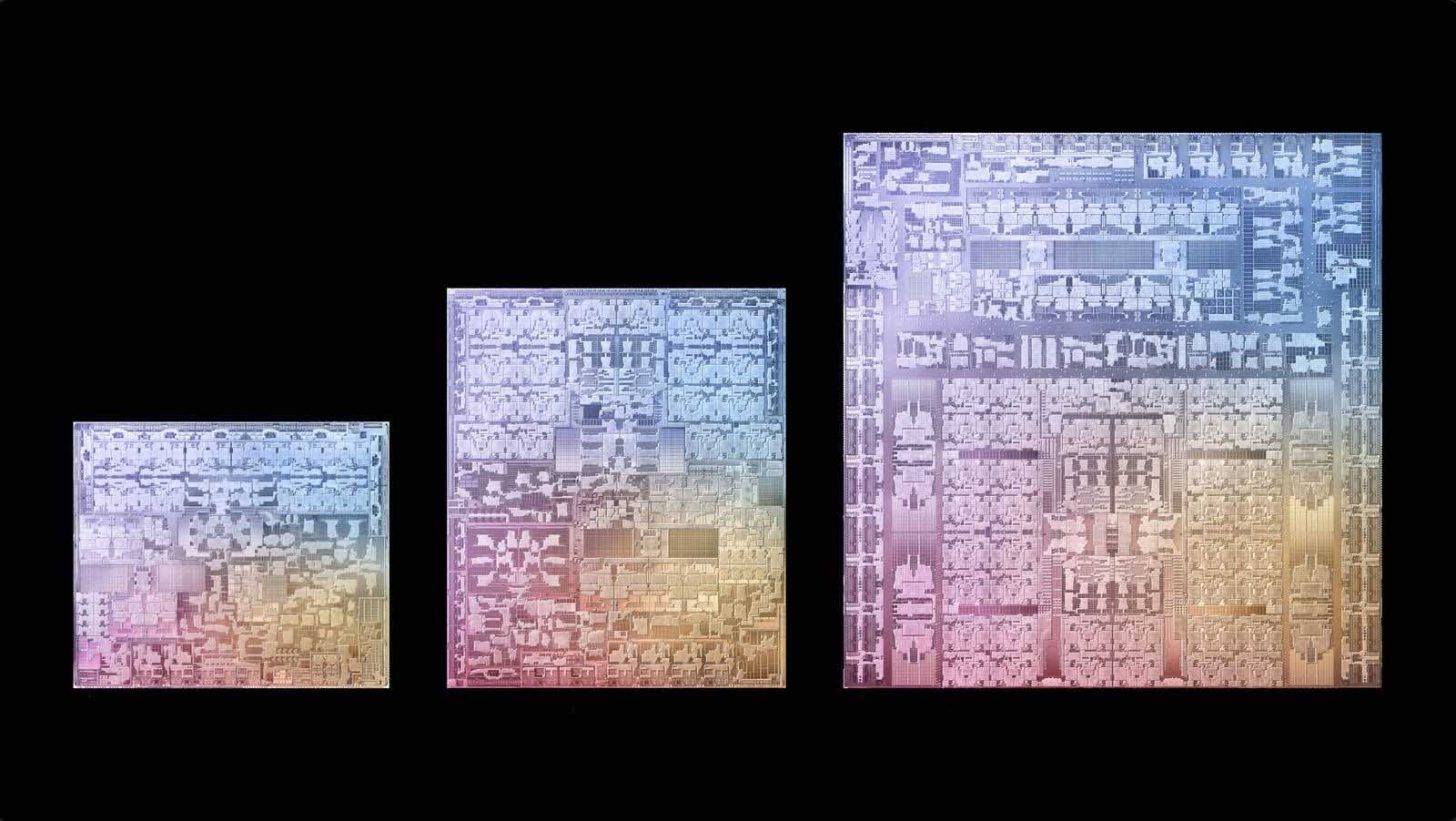
▲ 图|Wccftech
至于硬件外观方面,M5 Pro 和 M5 Max 版 MacBook Pro 不会有任何新变化,想要用上双层 OLED 的 MacBook Pro 起码要等到 2027 年后了。
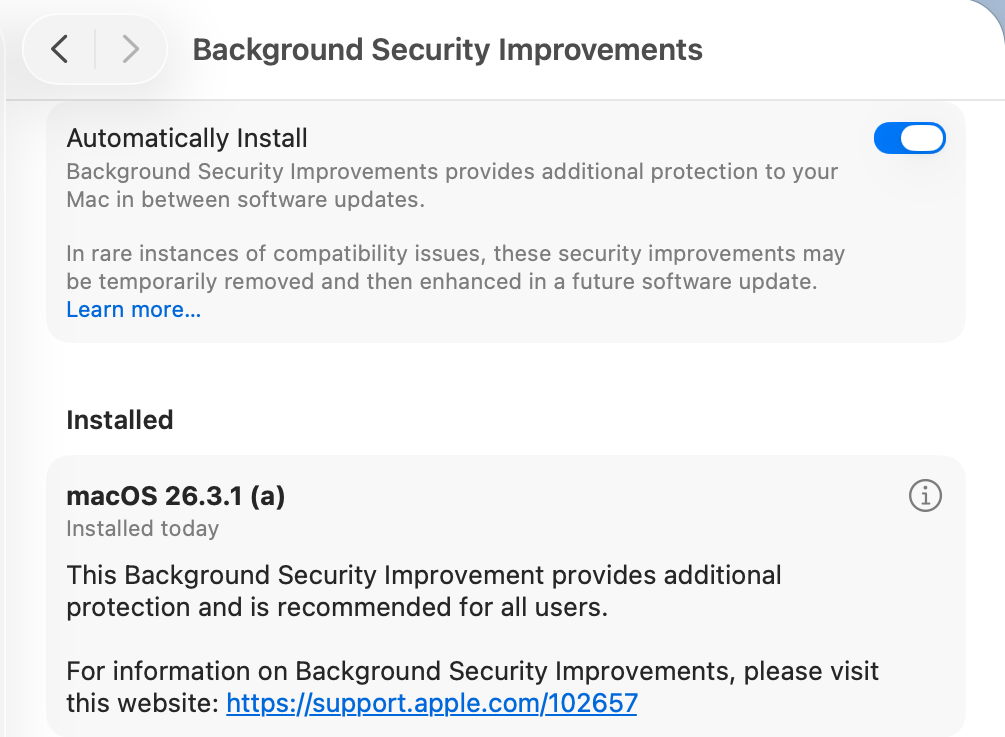
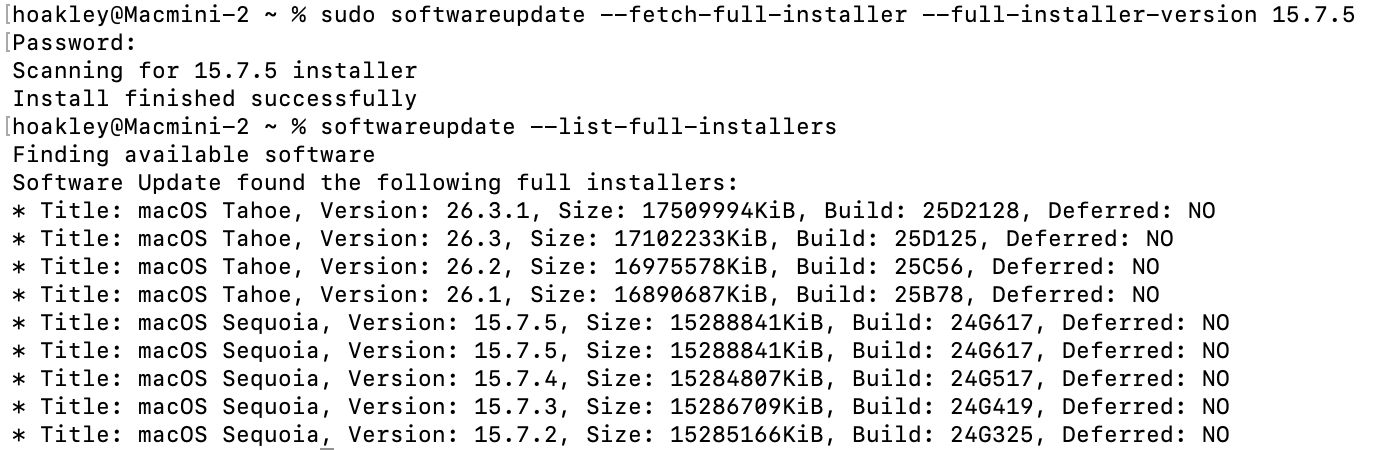
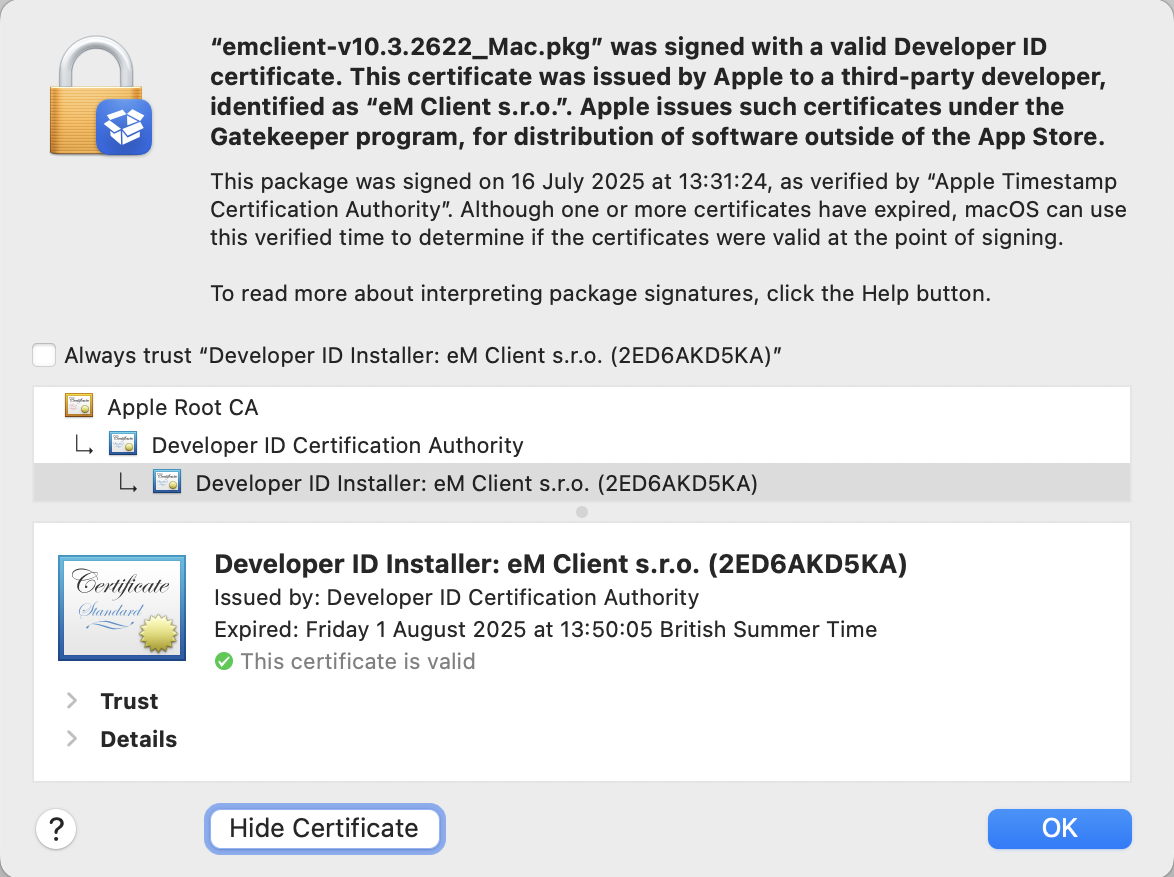
新 iPad 和 iPad Air:评为 NPC
除了前面几款相对令人兴奋的新品,这次发布会上我们还会看到入门款 12 代 iPad 和换处理器的新 iPad Air。
目前来看,12 代 iPad 将会搭载标准版 A18 处理器,iPad Air 则是如期从现在的 M3 升级到 M4,其余参数基本保持不变。
预计新 iPad Air 的模具也不会有变化。这有点尴尬:iPad Air 的其实比 iPad Pro 还要厚,如果模具不更新的话,只能评为 NPC 了……

▲ iPad 11 代|ESR
不过至少,A18 芯片意味新款 iPad 终于补齐了 Apple Intelligence 的入门标准,可以「为 Apple 智能准备好」了。
这样一来,苹果算是补上了 AI 布局最后一块拼图,实现了自家 3C 产品线的全面 AI 化——
只是这个 AI 我们究竟什么时候能用上,依然是个悬而未决的问题。
▲ 图|Apple
让人失望的是,传说中的 OLED iPad mini 大概无缘本次发布会,甚至有可能进一步被延期到 2027 年。
看隔壁「等等党」的遭遇,或许「游戏党」们可以不用再犹豫了,现在趁着补贴入手一个 iPad mini 7 或许就是最划算的选择。
其他硬件:周边大换代
实际上,本次春季发布会对于 Mac 用户来说是个难得的好日子。
除了前面几款光环下的产品之外,我们更有可能见到 M5 的大普及时代。
比如先后受到国补、教育优惠、OpenClaw 浪潮助推的 Mac mini,就有可能趁着本次发布会上架 M5/M5 Pro 款。
如果属实,这将会是最适合部署 OpenClaw 或其它本地 agent,以及面向本地模型推理用途的入门机型。

▲ 图|zeera wireless
而 Mac Studio 则会跟着 MacBook Pro 一起更新 M5 Pro/Max 处理器——但如果你需要 Ultra 级别的性能,苹果上一代的 Ultra 芯片只升级到了 M3,这次能有 M4 Ultra 就不错了。
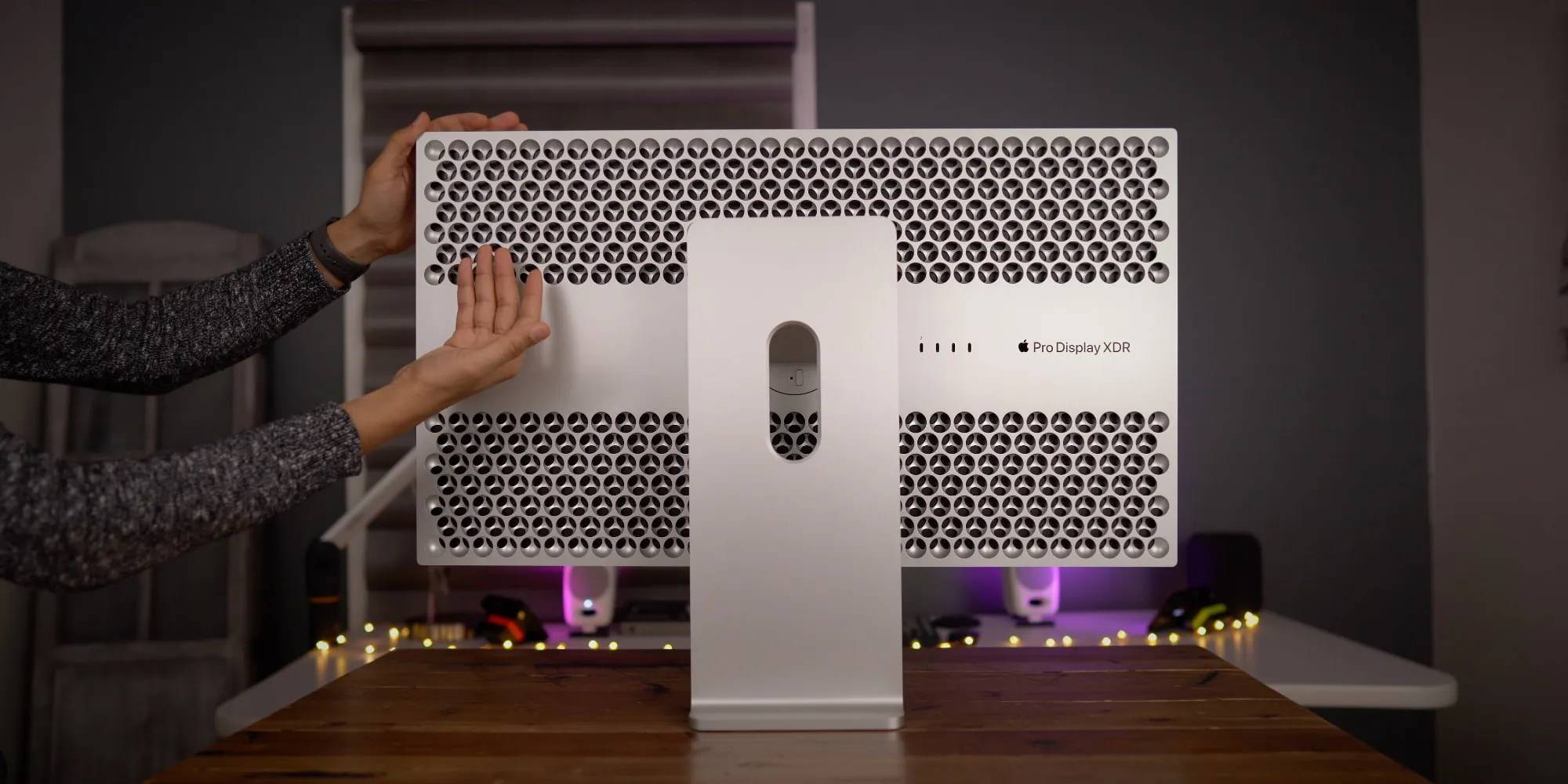
给专业创作者的好消息:搁置了许多年没更新的苹果显示器产品线,也有望在这个春天得到升级。

▲ 图|TechRadar
根据此前彭博社爆料,新款 Studio Display 将会和 M5 Pro/Max 款 Mac 共同推出。
而在一月份,我们的确在中国能效标识网上看到了「美国苹果公司高性能 LCD 显示器」:

参考今年 CES 上,LG 展示的 2304 分区 27 寸 5K 165Hz Mini LED 显示器,这次的 Studio Display 2(猜测名称)估计就会用上同款面板。
而根据 MacWorld 从 macOS 中挖掘到的代码,今年的新款显示屏都支持最高 120Hz ProMotion 可变刷新率。
属于 Studio Display 和 Pro Display XDR 的高刷时代终于来了。
▲ 图|9to5Mac
此外,新的 Studio Display 还会用上 iPhone 17 同款的 A19 处理器,主要用于给内容解码、摄像头 Central Stage、扬声器空间音频提供算力支持——
好么,一台手机的 SoC,放进显示器作为协处理器,真是倒反天罡!(开个玩笑)
HomePod、HomePod mini 和 AppleTV 这「家居三剑客」预计也会在这次发布会上迎来升级。
坏消息是,传说中那个带屏幕的 HomeHub 以及智能家居操作系统 homeOS 大概率依然是传说,最新信源均表示苹果搁置或取消了这个智能家居中枢计划,选择继续将功能与现有产品集成。

▲ 图|zeera wireless
其中,新款 HomePod 和 HomePod mini 不出意外将会迎来几个新配色,以及手表同款的 S10 处理器,从而对更先进的空间音频、蓝牙 5.3 和第二代 UWB 芯片提供支持。
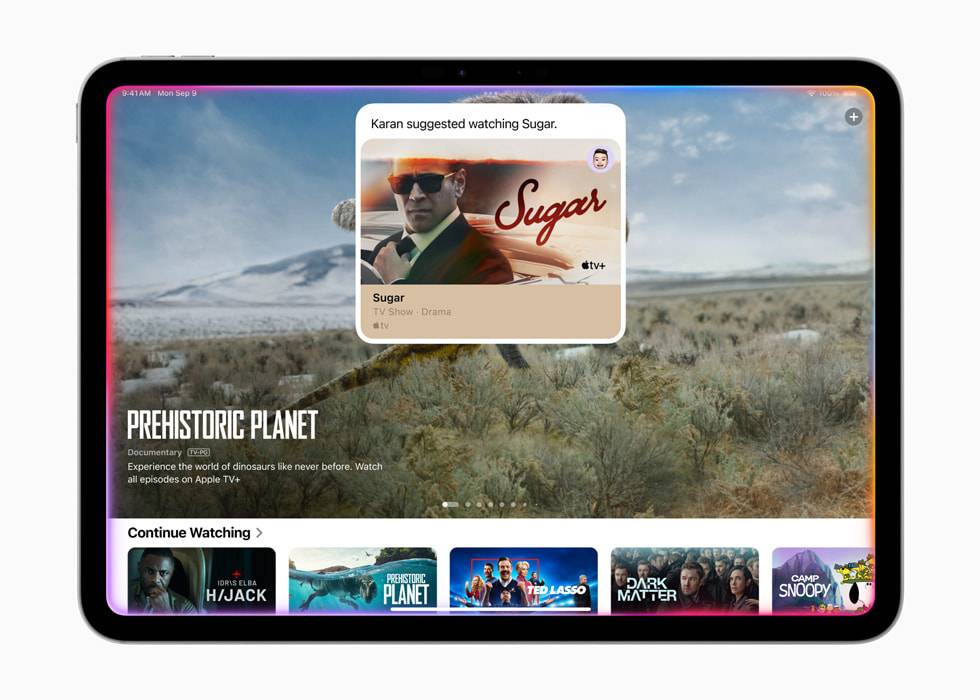
对于新款 Apple TV 来说,大部分升级都集中在 tvOS 上面。
根据 9to5Mac 的报道,tvOS 26.4 中,原本独立的 iTunes 和 Movies 应用将会合并,让用户购买音乐和影片的体验更加无感一些。

▲ 图|9to5Mac
另外,tvOS 26.4 还优化了更换 CC 字幕样式的操作。新增的「样式」菜单允许用户在数种字幕字体和风格之间快速切换,不需要退出正在播放的视频。
另有消息指出,今年的新 Apple TV 可能会分成 4K 和 4K Pro 两款。
区别在于 Apple TV 4K Pro 可能会提供把自己作为 Wi-Fi mesh 节点的功能,以及最高 4K 120Hz 的视频规格。
新的 Apple TV 预计会用上最新的 A19 处理器,8GB 内存,硬盘则从 128GB 起步进化到了 256GB 起步——说不定就是旁边 iPhone 17 的同款备料。

▲ 图|CNET
总的来说,2026 年的苹果春季发布会不仅是之前从未有过的新形式,更是最近几年里新品数量最多的一次。
对于其中 MacBook、MacBook Pro、新 iPad 和 Studio Display 等等,爱范儿的建议依然是相同的:
明确需求,该买就买,买新不买旧。
iPhone 17 系列乘上了 2025 年末内存涨价的最后一班车,能够在今天保持住相当的价格优势。

而今年春季的这一波新品,虽然其中几款的价格会迎来小波动,但整体受到内存涨价的冲击相对较小——
苹果体量大、利润空间高的特性,在这一刻变成了直接的商业优势。
因此,爱范儿觉得,如果上面的新品有契合到你的换新需求,那么现在入手会比 618 入手带来更大的价格优势。
#欢迎关注爱范儿官方微信公众号:爱范儿(微信号:ifanr),更多精彩内容第一时间为您奉上。
爱范儿 |
原文链接 ·
查看评论 ·
新浪微博

 点击图片播放视频
点击图片播放视频 本期关联播客
本期关联播客